CVE-2015-7547 glibc vulnerability
In the past few days Google has identified a vulnerability in glibc (GNU C Library). It allows attackers to crash processes and potentially run code remotely on your server.
The vulnerability itself is best described by the Google Security Team’s blog-post. To summarise:
“The glibc DNS client side resolver is vulnerable to a stack-based buffer overflow when the getaddrinfo() library function is used. Software using this function may be exploited with attacker-controlled domain names, attacker-controlled DNS servers, or through a man-in-the-middle attack… …Remote code execution is possible, but not straightforward.”
glibc is a library which provides many basic functions and system calls to C programs. Since libraries are only loaded in when a program is started, this means that only daemonised (a process which is left running in the background) programs are effected. When those programs are restarted they will load in the new glibc library which mitigates the issue.
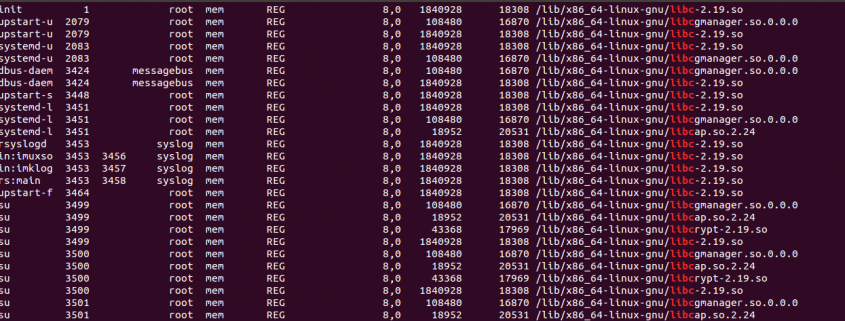
You can get a list of all programs using glibc by running a command such as:
sudo lsof | grep libc | cut -d' ' -f 1 | sort | uniq
This shows that glibc is tied into nearly every service on a typical Linux system. It can quickly become a large job to restart each process, especially in the correct order. The quickest way of doing this is by rebooting your server.
Our advice regarding this matter is:
- Ensure the latest glibc packages are installed.
- Reboot your server (or restart all processes that use glibc)









Trackbacks & Pingbacks
[…] The admin can search for dependant applications that maybe using a library that has been patched (i.e. glibc patches) […]
Leave a Reply
Want to join the discussion?Feel free to contribute!