Tripwire – How and Why
Open Source Tripwire is a powerful tool to have access to. Tripwire is used by the MOD to monitor systems. The tool is based on code contributed by Tripwire – a company that provide security products and solutions. If you need to ensure the integrity of your filesystem Tripwire could be the perfect tool for you.
What is Tripwire
Open Source Tripwire is a popular host based intrusion detection system (IDS). It is used to monitor filesystems and alert when changes occur. This allows you to detect intrusions or unexpected changes and respond accordingly. Tripwire has great flexibility over which files and directories you choose to monitor which you specify in a policy file.
How does it work
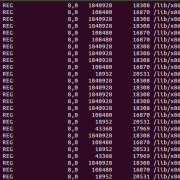
Tripwire keeps a database of file and directory meta data. Tripwire can then be ran regularly to report on any changes.
If you install Tripwire from Ubuntu’s repo as per the instructions below a daily cron will be set-up to send you an email report. The general view with alerting is that no news is good news. Due to the nature of Tripwire it’s useful to receive the daily email, that way you’ll notice if Tripwire gets disabled.
Before we start
Before setting up Tripwire please check the following:
- You’ve configured email on your server. If not you’ll need to do that first, we’ve got a guide.
- You’re manually patching your server. Make sure you don’t have unattended upgrades running (see the manual updates section) as unless you’re co-ordinating Tripwire with your patching process it will be hard for you to distinguish between expected and unexpected changes.
- You’re prepared to put some extra time into maintaining this system for the benefit of knowing when your files change.
Installation on Ubuntu
sudo apt-get update sudo apt-get install tripwire
You’ll be prompted to create your site and local keys, make sure you record them in your password manager.
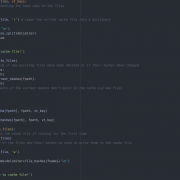
In your preferred editor open /etc/tripwire/twpol.txt
The changes you make here are based on what you’re looking to monitor, the default config has good coverage of system files but is unlikely to be monitoring your website files if that’s something you wanted to do. For example, I’ve needed to remove /proc and some of the files in /root that haven’t existed on systems I’ve been monitoring.
Then create the signed policy file and then the database:
sudo twadmin --create-polfile /etc/tripwire/twpol.txt sudo tripwire --init
At this point it’s worth running a check. You’ll want to make sure it has no errors.
sudo tripwire --check
Finally I’d manually run the daily cron to check the email comes through to you.
sudo /etc/cron.daily/tripwire
Day to day usage
Changing files
After you make changes to your system you’ll need to run a report to check what tripwire sees have changed.
sudo tripwire --check
You can then update the signed database. This will open up the report allowing you to check you’re happy with the changes before exiting.
sudo tripwire --update -r /var/lib/tripwire/report/$HOSTNAME-yyyyMMdd-HHmmss.twr
You’ll need your local key in order to update the database.
Changing policy
If you decide you’d like to monitor or exclude some more files you can update /etc/tripwire/twpol.txt. If you’re monitoring this file you’ll need to update the database as per the above section. After that you can update the signed policy file (you’ll need your site and local keys for this).
sudo tripwire --update-policy /etc/tripwire/twpol.txt
As you can see tripwire can be an amazingly powerful tool in any security arsenal. We use it as part of our maintenance plans and encourage others to do the same.







Leave a Reply
Want to join the discussion?Feel free to contribute!